Blue Team Labs Online - Covert

Incident Response
Tags: Wireshark PowerShell Editor T1048.003 T1071.001
Scenario We got you the network capture of one of the compromised Windows server. Investigate the traffic and figure out the attacker actions.
Environment Awareness
Evidence Discovery
Look like we only have pcap file as a sole evidence on this investigation so lets start the investigation right away by open this file on Wireshark.
Investigation
Q1) What is the domain name used in exfiltration?
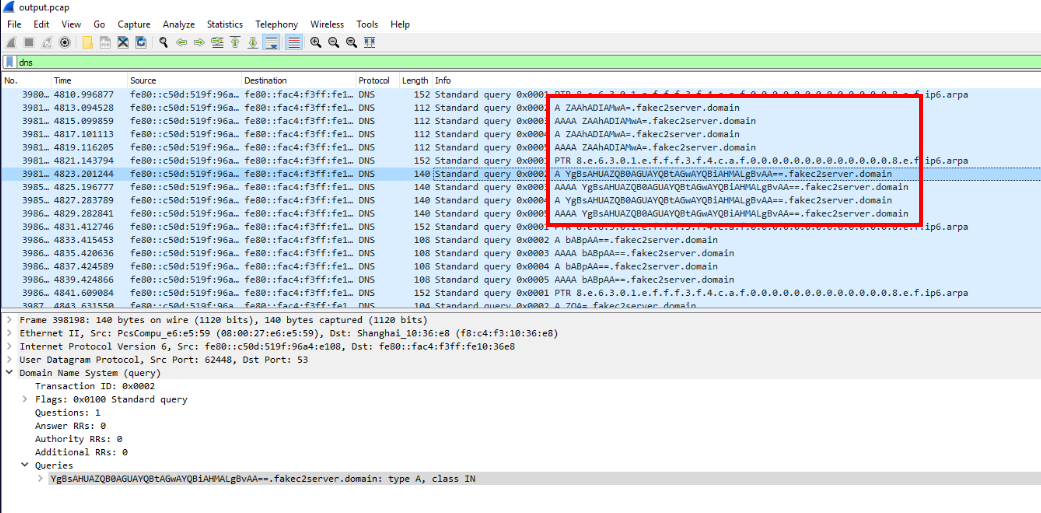
First, we can filter with dns for DNS traffic which we will see the suspicious domain that has base64 decoded subdomain.
Then we can use dns && dns.qry.name contains "fakec2" then we will see several DNS queries associated with this domain name and this is the answer we are looking for.
Answer
fakec2server.domainQ2) What are the passwords that has been exfiltrated? User stored the passwords in a file as of format: password1 site1 password2 site2
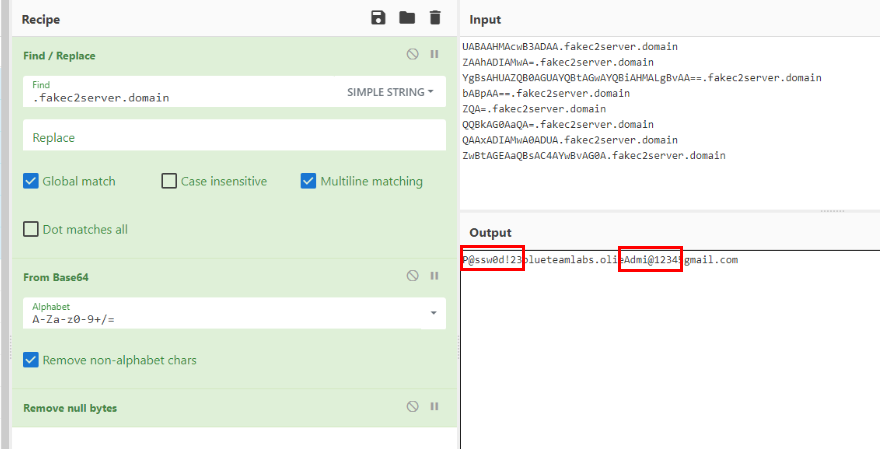
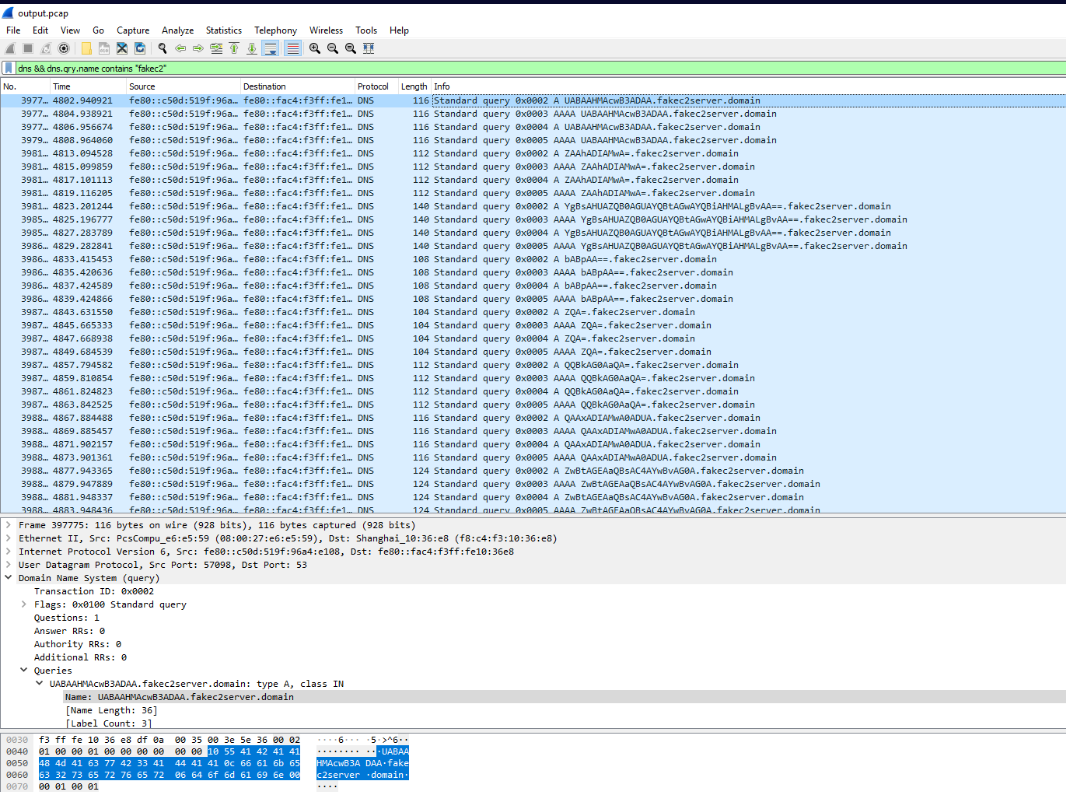
Utilizing CyberChef then we can copy requested domains from pcap file then use "Find / Replace" to remove latter part which will only have base64 encoded string left then we can use "From Base64" to decode it
And now we can see 2 passwords were exfiltrated via DNS.
Answer
P@ssw0d!23, Admi@12345Q3) There are lot of suspicious traffic to the system before the exfiltration. From which IP do you see port scan traffic?
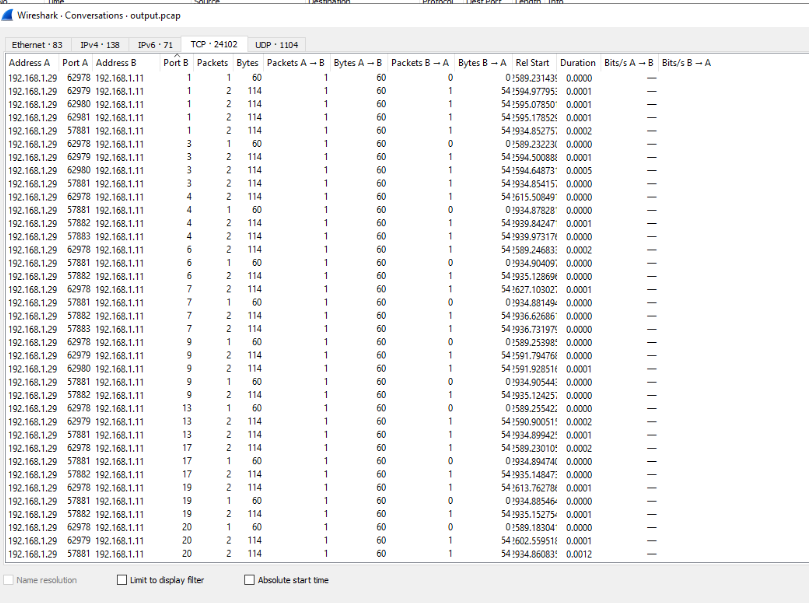
Since there are so many packets within this pcap file then we can use "Conversations" statistics and sort by port which we can see that 192.168.1.29 sent many packets start to port 1,2,3,4 and so on, indicating that this IP address was conducted port scanning on 192.168.1.11
Answer
192.168.1.29Q4) Attacker used a covert command execution over HTTP. Both command and its output are encrypted and stored in a variable/parameter in the format – parameter=
. Find the parameter that was used in request from infected system to the c2 server
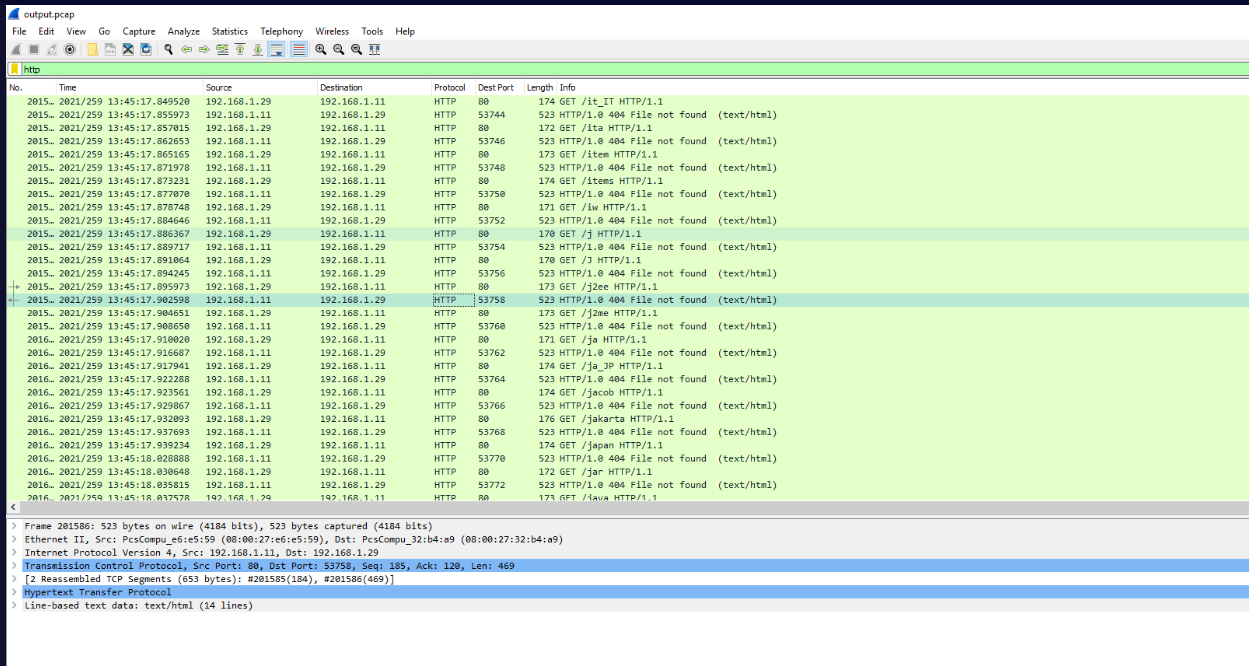
Look like the attacker discovered website running on the targeted system so the attacker conducted directory bruteforcing next which we will have to filter these out to find the traffic that we are looking for.
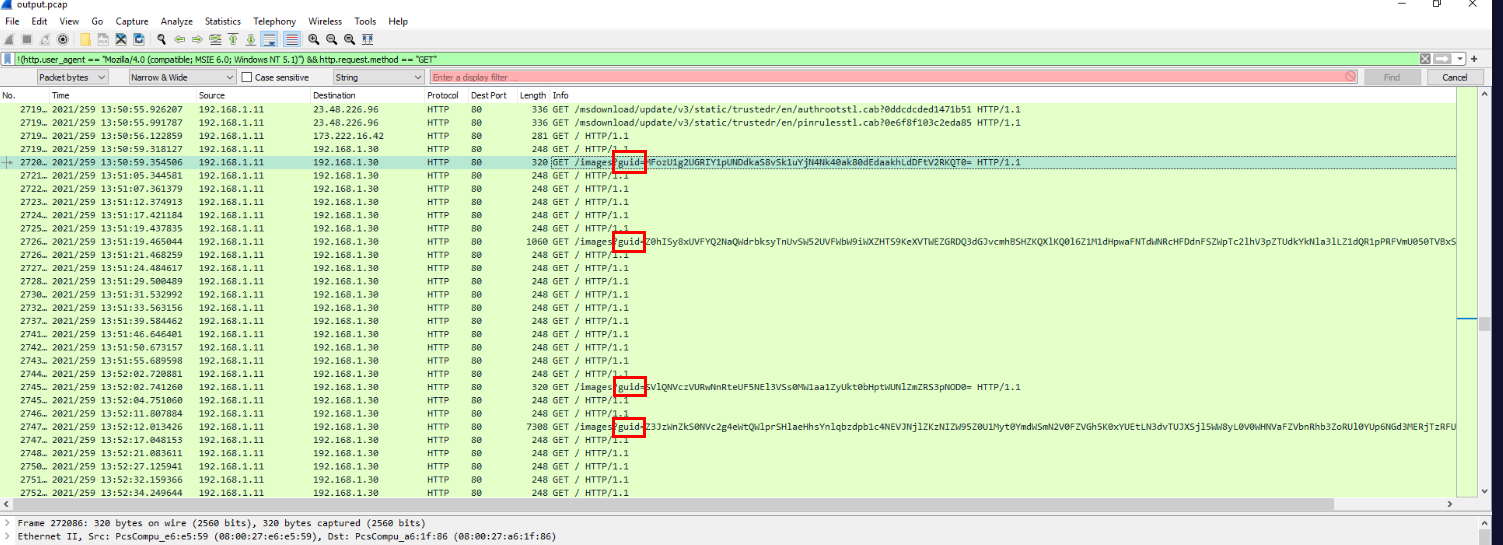
By filtering with !(http.user_agent == "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1)") && http.request.method == "GET" and we will have only HTTP GET request which is not share the same user agent as the directory bruteforcing user agent.
Then we can see the parameter guid was used to request something from 192.168.1.30 which likely to be a C2 server.
Answer
guidQ5) Similarly, what is the parameter that was used in response?
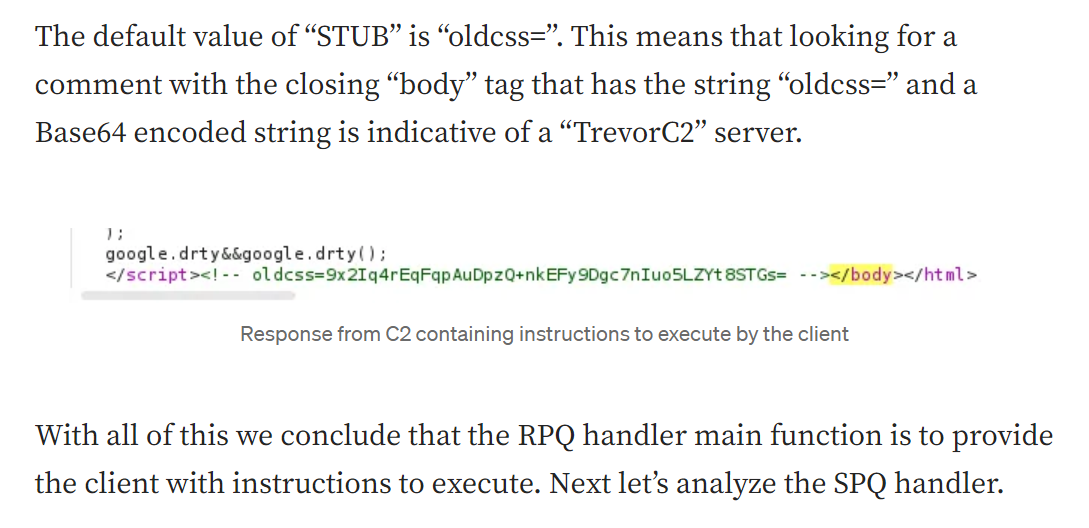
After some research then we will eventually find that those HTTP communication are characteristics of Trevor C2 framework and Nasreddine's has a good write-up about this framework here what he summarized about this C2 framework
"So basically this framework will clone any website and inject commands sent by the C2 within its body. The client will then read the command(s) execute them and send the results back to the server." - Nasreddine Bencherchali
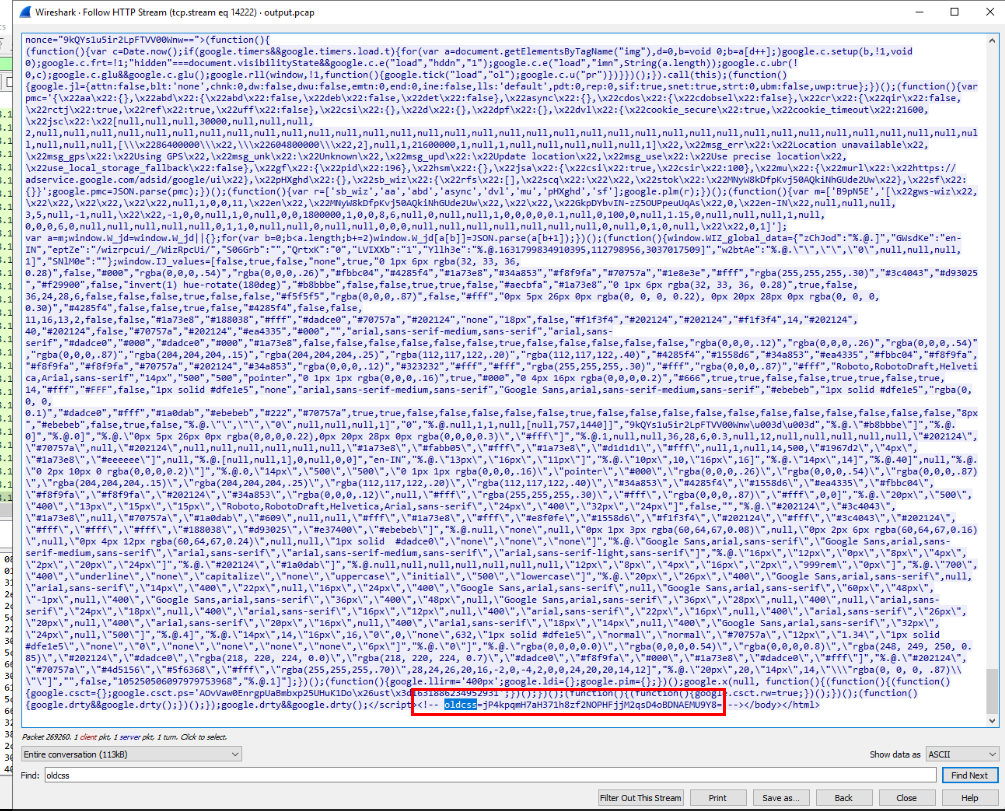
This C2 framework is oldcss in the comment as default and the value assign to this parameter (in the comment) is the instruction/command for client to execute.
Answer
oldcssQ6) Use some OSINT skills with these parameters and figure out the c2 framework that the attacker used.
Answer
TreverC2Q7) Understand the encryption and working of the c2 communication and try to decrypt the commands and output. What is the first command sent by the attacker?
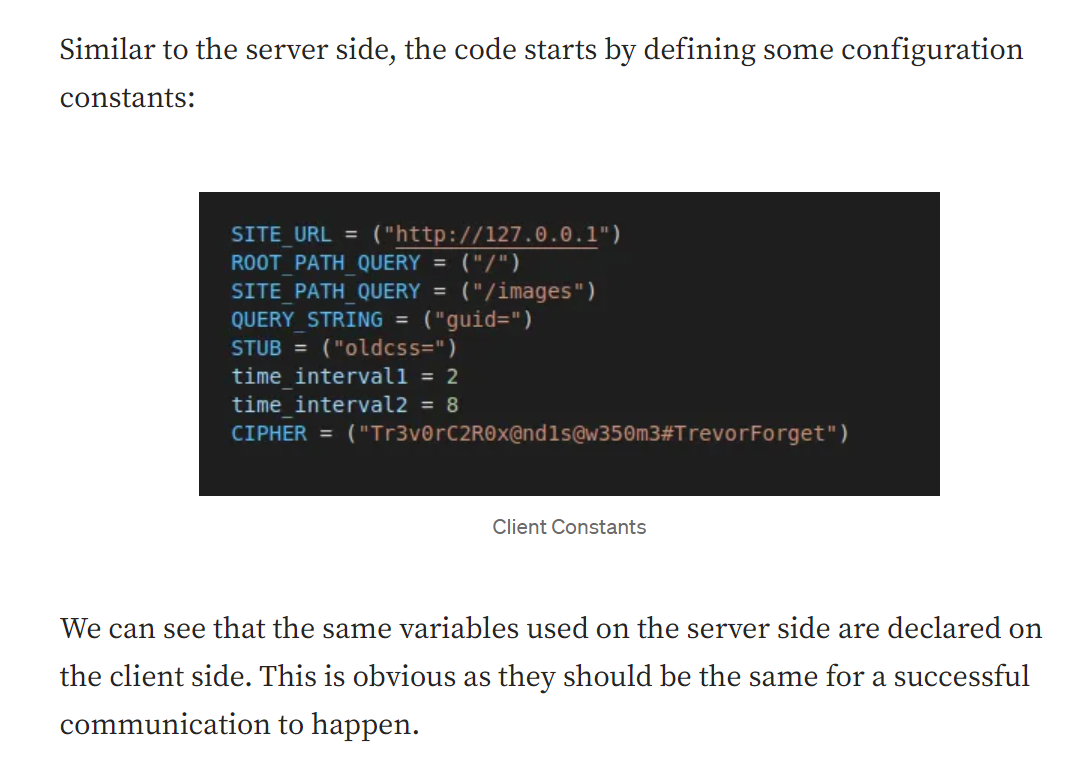
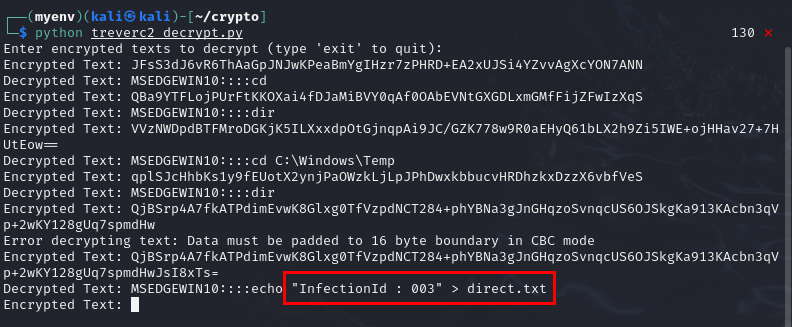
One more thing to about this C2 is, its open-source C2 framework and its even hard-coded AES key
Tr3v0rC2R0x@nd1s@w350m3#TrevorForget
Then after more research, there is someone who created decrypting script for this C2 framework which was once used as a CTF challenge in UofTCTF 2024
When decoded, it splits into: - IV: The first 16 bytes of the decoded data. - Ciphertext: The remaining bytes of the decoded data.
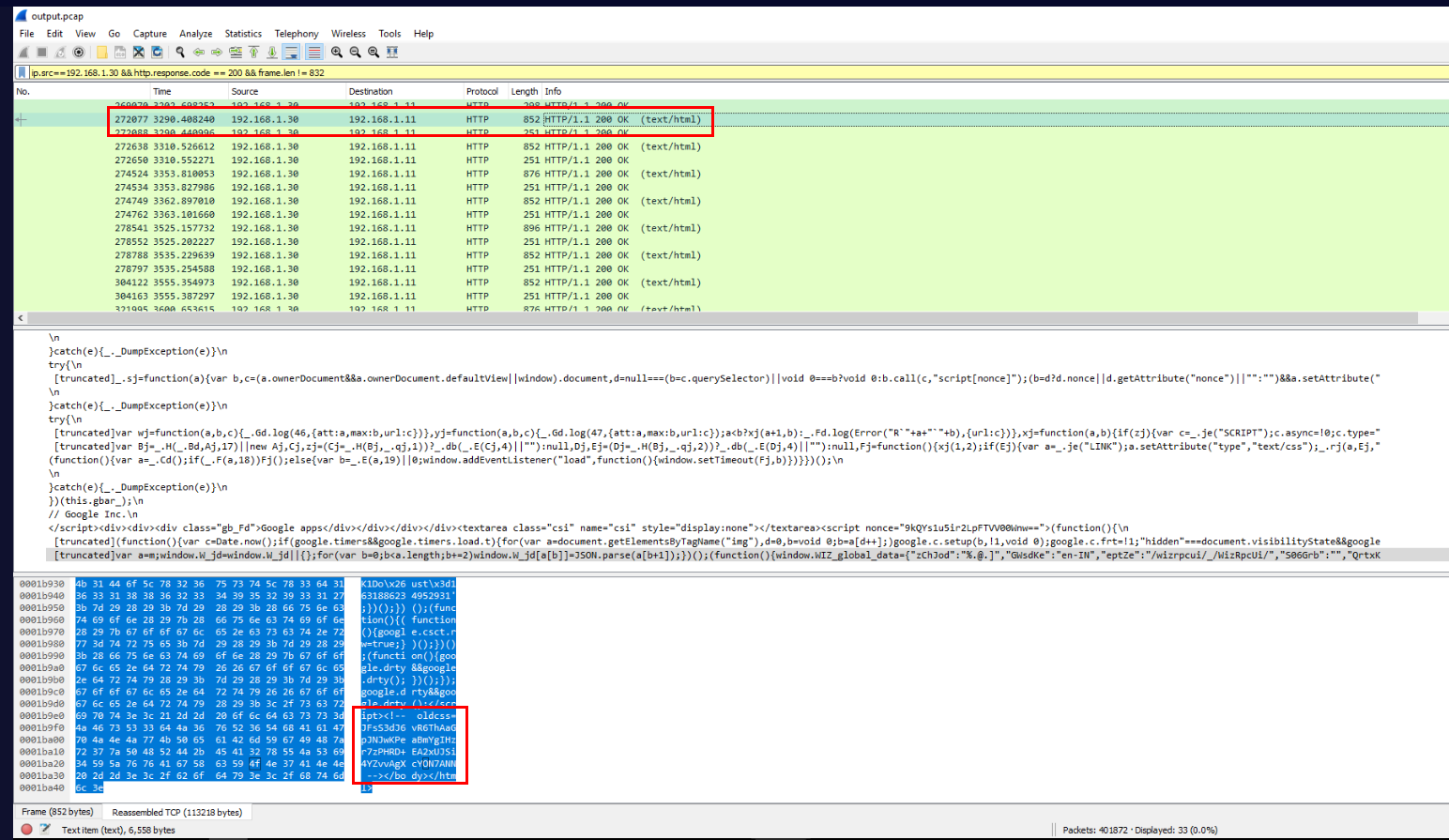
Lets use ip.src==192.168.1.30 && http.response.code == 200 && frame.len != 832 filter to get HTTP response request from the attacker's C2 which contains the instruction for the victim to execute inside oldcss variable as shown on the image above.
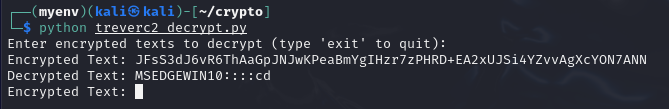
I also modified the script to recursively run until I type "exit", then we can see that the first command sent by the attacker is cd (change directory)
Answer
cdQ8) Attacker created a text file and marked a infection ID in the system. What is the infection ID?
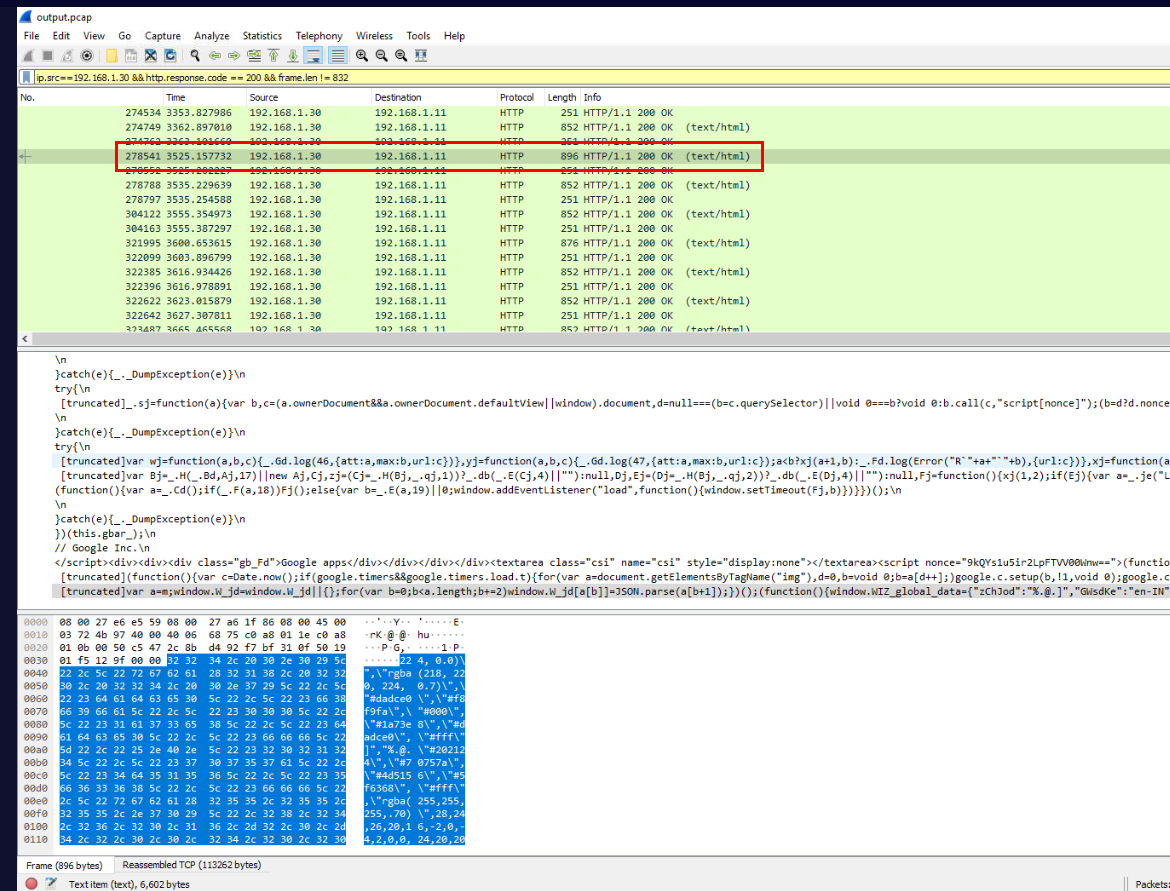
Since, we could not export the pcap file out of the investigation machine so we will have to manually copy the the value of each oldcss variable return from the attacker's C2 then we will finally have the ciphertext we need for this question in frame 278,541
Then we can see that the attacker echo the infection ID to a text file.
Answer
003Q9) Attacker invoked a PowerShell script to do the data exfiltration. What is the name of the PowerShell script?
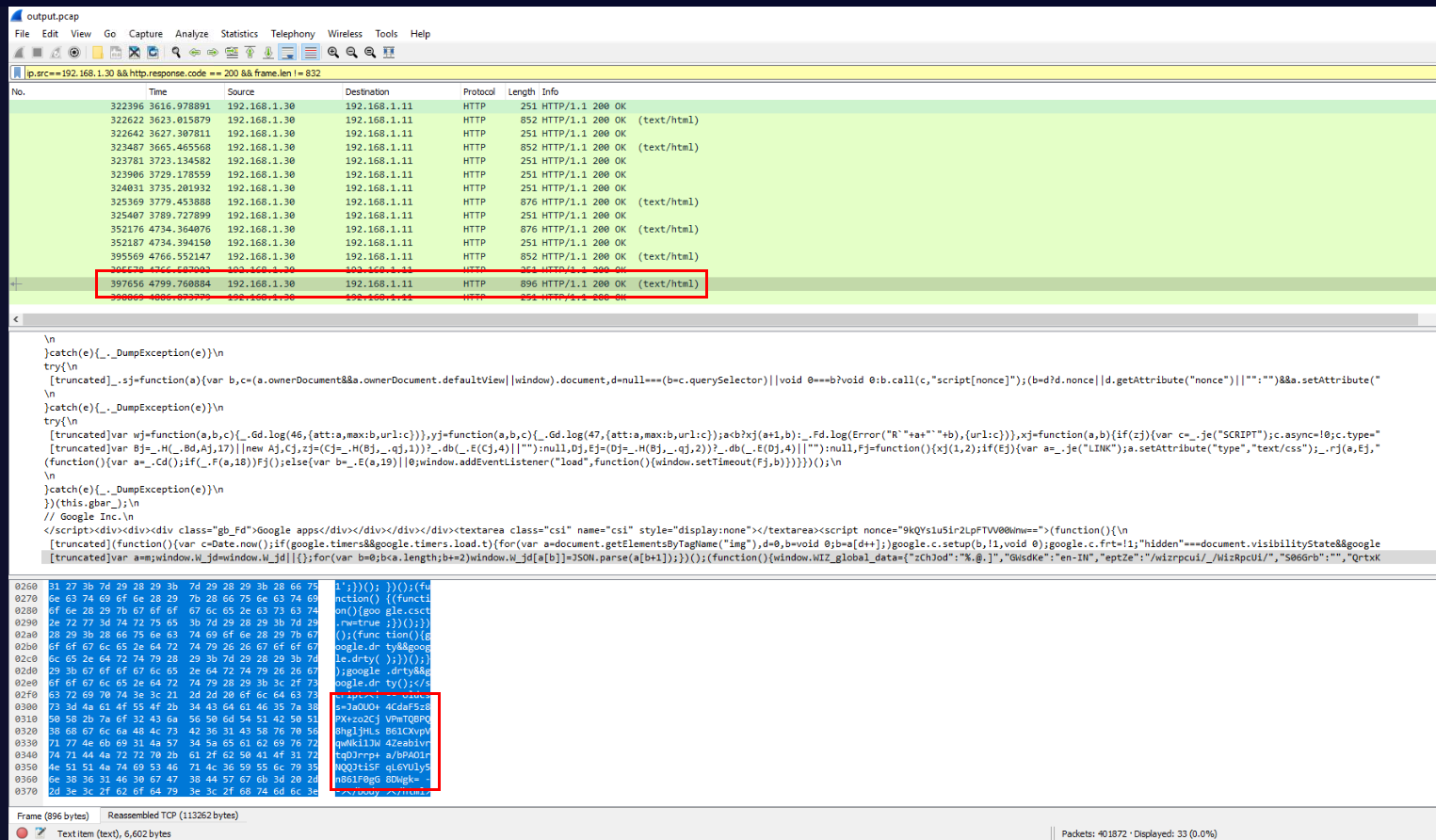
Now after continue to decrypt more communication then we will finally have the one we are looking for in frame 397,656
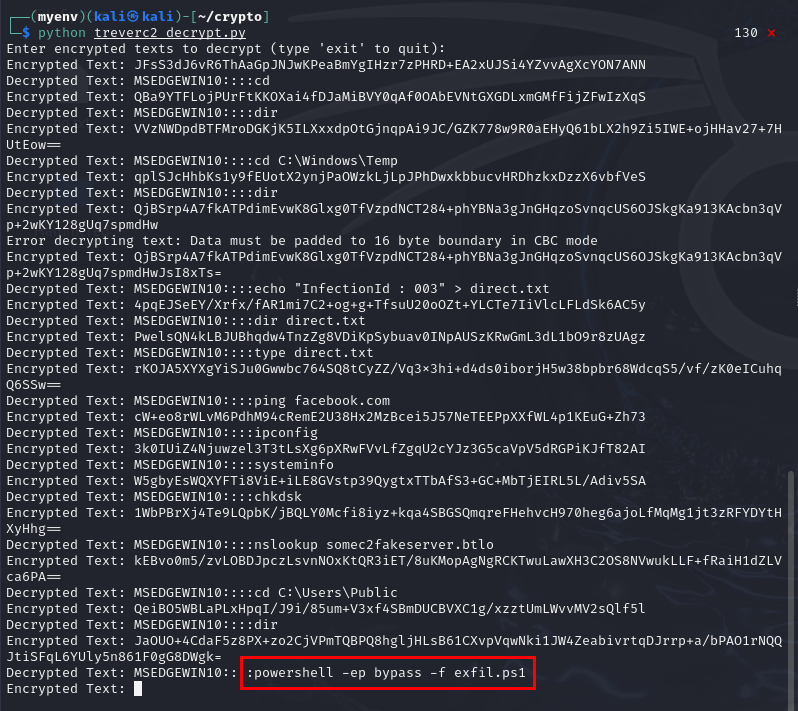
Which is a PowerShell bypass execution policy command to execute exfil.ps1 script which is the script responsible for data exfiltration via DNS we found on the Q1-2
Answer
exfil.ps1 https://blueteamlabs.online/achievement/share/52929/79
https://blueteamlabs.online/achievement/share/52929/79